Kodi Addons Linked to Malicious Cryptomining Campaign

The Dutch developer and administrator of XvBMC-NL was visited by bailiffs in July and soon after the repository shut down. BREIN offered to settle the matter for 2,500 euros as long as the admin known as ‘Z’ signed an abstention agreement.
Months earlier, however, the XvBMC-NL repo was an unwitting participant in a campaign to infect Kodi users with cryptocurrency-mining malware, security firm ESET reports.
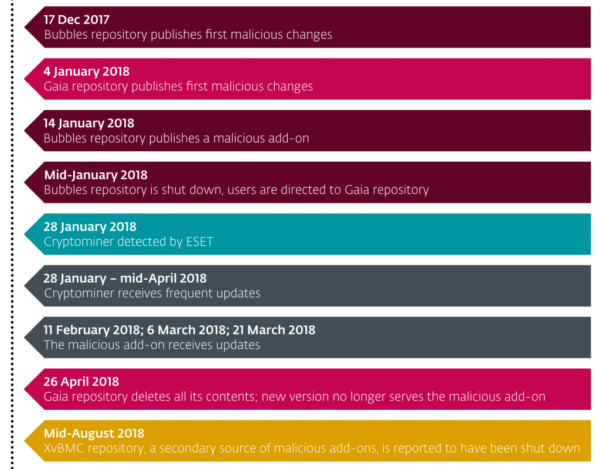
“According to our research, the malware we found in the XvBMC repository was first added to the popular third-party add-on repositories Bubbles and Gaia (a fork of Bubbles), in December 2017 and January 2018, respectively,” ESET writes.
“From these two sources, and through update routines of unsuspecting owners of other third-party add-on repositories and ready-made Kodi builds, the malware spread further across the Kodi ecosystem.”
ESET reports that the malware has a multi-stage architecture and uses techniques to hide the fact that the cryptominer came from a malicious addon. The miner, which is Monero-based, runs on Windows and Linux only, a relief to Android and macOS users who appear to be unaffected.
The three potential infection routes appear to be fairly cunning, ESET notes.
1. [Users] add the URL of a malicious repository to their Kodi installation so as to download some add-ons. The malicious add-on is then installed whenever they update their Kodi add-ons.
2. [Users] install a ready-made Kodi build that includes the URL of a malicious repository. The malicious add-on is then installed whenever they update their Kodi add-ons.
3. [Users] install a ready-made Kodi build that contains a malicious add-on but no link to a repository for updates. They are initially compromised, though receive no further updates to the malicious add-on. However, if the cryptominer is installed, it will persist and receive updates.
Further analysis by ESET shows that the top five countries affected by the threat are the United States, Israel, Greece, the United Kingdom and the Netherlands.
With the Bubbles repo now down, that is no longer a source for the malware. Gaia, ESET reports, is no longer serving the malicious code either. However, Kodi users who were infected could still have the malware on their machines and there’s a risk that other repos and Kodi builds could be distributing the code, “most likely” without their knowledge.
Timeline of the attack, as per ESET
A very detailed technical analysis of the attack has been published by ESET along with instructions on how users can discover if they’re affected.
“To check if your device has been compromised, scan it with a reliable anti-malware solution. ESET products detect and block these threats as Win64/CoinMiner.II and Win64/CoinMiner.MK on Windows and Linux/CoinMiner.BC, Linux/CoinMiner.BJ, Linux/CoinMiner.BK, and Linux/CoinMiner.CU on Linux,” the company reports.
“On Windows you can use the ESET Free Online Scanner, and on Linux the free trial of ESET NOD32 Antivirus for Linux Desktop, to check your computer for the presence of these threats and remove anything that is detected. Existing ESET customers are protected automatically.”
While the attack is undoubtedly serious, at the time of writing its reach appears to be limited. By examing the malware authors’ Monero wallet, ESET estimates that a minimum of 4,774 users are infected. Between them they have unwittingly generated around 5,700 euros or $6,700 for the attackers.
As ESET notes, Kodi malware is very rare. Aside from the case detailed above and the DDoS attack carried out briefly by an addon and reported here on TF, no other evidence of malware being distributed via Kodi addons has been reported.
Source: TF, for the latest info on copyright, file-sharing, torrent sites and more. We also have VPN reviews, discounts, offers and coupons.




Leave a Reply
Want to join the discussion?Feel free to contribute!