
To help solve this problem, in 2009 US-based Kickstarter was born, a site that has developed into a global crowdfunding platform where anyone can throw a few dollars at projects they believe could enjoy future success.
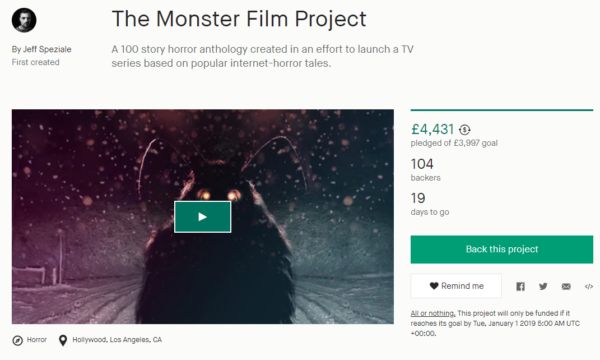
According to current stats, the site has received pledges exceeding four billion dollars from more than 15.5 million backers, which have funded more than 155,000 individual projects. One of those is campaign formerly known as The Monster Book of Monsters Film Project.
“THE MONSTER BOOK OF MONSTERS is a collection of 100 stories from around the world, inspired by the legendary book from the Harry Potter universe,” the Kickstarter read until recently.
“These aren’t your everyday Werewolves and Wendigos either. Each story is told by the survivor of an encounter with a unique and mysterious creature more wild and varied than you can imagine. From the twisted minds of 70 authors including Amazon Best Sellers: Tobias Wade, Blair Daniels, Tara Devlin, and P.F. McGrail. As well as numerous Reddit NoSleep award winners.”
The idea of the campaign is to raise funds that will go towards a ‘sizzle reel’, a short video highlighting a vision and tone for a proposed movie or TV show.
“This reel will be pitched to large production companies in an effort to launch a horror inspired anthology TV series. The more money raised- the better the reel!” the Kickstarter reads.
The campaign had a modest target of just $3,997 dollars, which was easily reached a few days ago and well in advance of the January 1, 2019 deadline. However, the project appears to have landed on the radar of Warner Bros. who expressed displeasure at the Harry Potter references in the fundraiser.
In a takedown notice sent to Kickstarter, the movie company alleged copyright infringement by the campaign due to its use of a book title featured in the movie Harry Potter and the Prisoner of Azkaban.
Citing itself as the owner of “The Harry Potter series of books and motion pictures, and all elements contained therein. Including, but not limited to, the ‘Monster Book of Monsters’,” Warner demanded action from the crowd-funding platform.
“This project identifies itself as ‘inspired by the legendary book from the Harry Potter universe’ and uses the original title created by Ms. Rowling,” Warner complained.
While it’s unclear whether Kickstarter temporarily took the campaign down, the complaint from Warner certainly prompted the team behind it into action. References to all things Harry Potter have now been removed, as the image below shows.
Additionally, the text proclaiming that “THE MONSTER BOOK OF MONSTERS is a collection of 100 stories from around the world, inspired by the legendary book from the Harry Potter universe” has now been transformed into a more basic “collection of 100 horror stories from around the world.”
Finally, the campaign has also amended its end goal statement. That was originally to have a “‘NoSleep’ inspired TV show”, a reference to Reddit’s NoSleep sub where people share their own scary stories. The edited aim is to have a straightforward “horror TV show”, although references to Reddit elsewhere in the campaign remain.
Warner Bros. are notoriously protective over their lucrative Harry Potter interests. Earlier this year the company’s lawyers told an annual Harry Potter festival held in Denmark that it could no longer use names and images related to the Harry Potter movies.
In 2009, Warner Bros. took action against a London-based single-mother after she dared to organize a Harry Potter-themed Halloween dinner. It’s unclear whether the sarcastically rebranded “Generic Wizard” night managed to sell out as planned.
Source: TF, for the latest info on copyright, file-sharing, torrent sites and more. We also have VPN reviews, discounts, offers and coupons.


 Following the example of the United States, the EU now has its very own piracy watch list.
Following the example of the United States, the EU now has its very own piracy watch list. 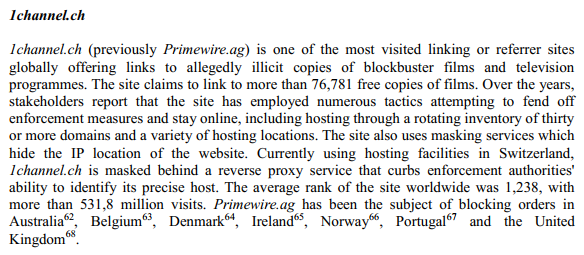


 Over the past two decades, the Software Alliance (BSA) has represented
Over the past two decades, the Software Alliance (BSA) has represented 
 At the start of the year the infamous hacking group Team Xecutor
At the start of the year the infamous hacking group Team Xecutor 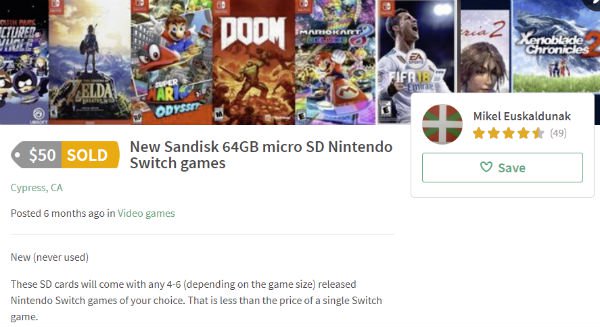


 This week we have two newcomers in our chart.
This week we have two newcomers in our chart.